Phishing Dark Waters: The Offensive And Defensi... -
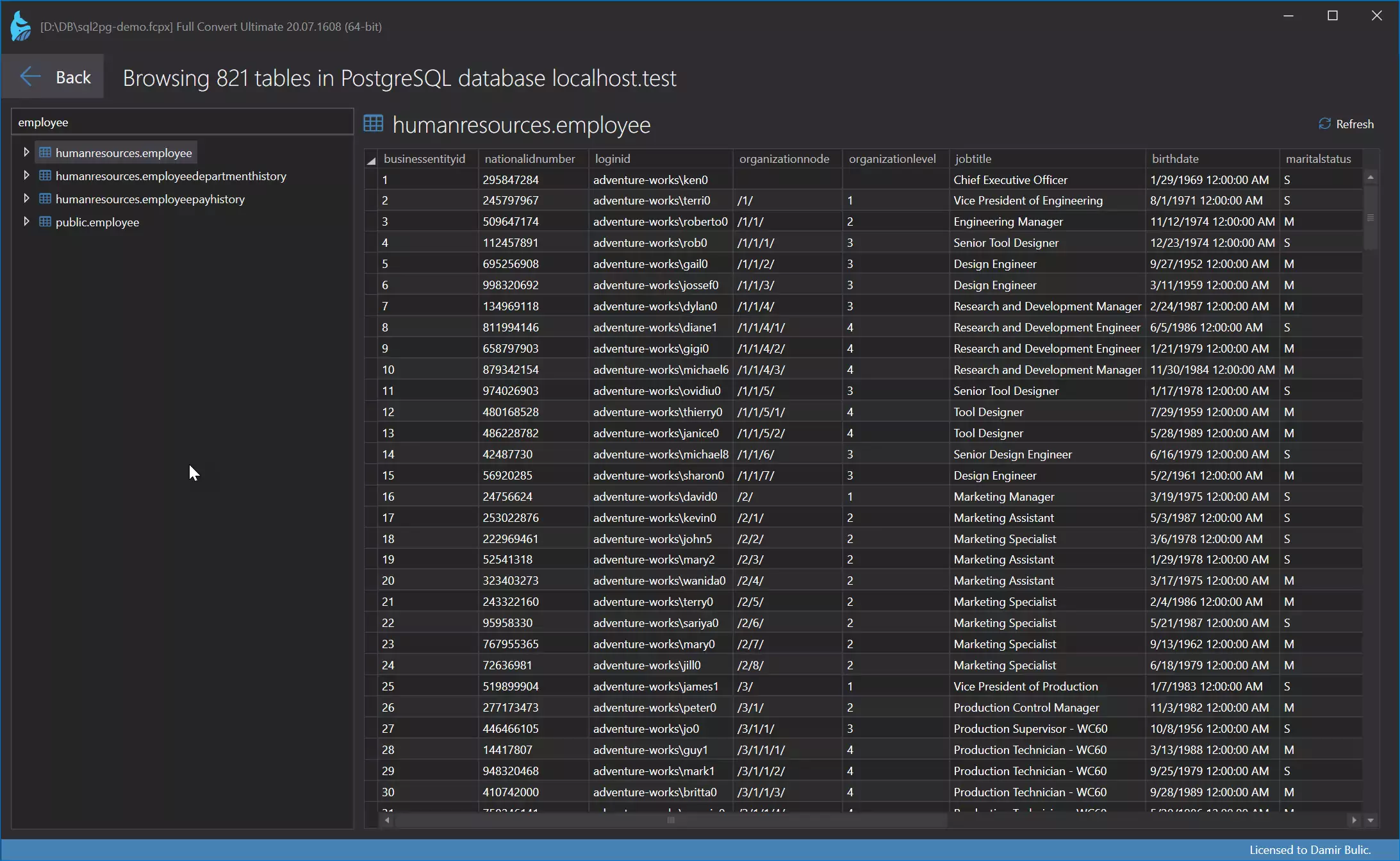
Full Convert is designed for ease of use and reliability to make sure you get your job done as quickly and as simply as possible.
CSV is also known as TSV, Flat file, Comma-separated text, TAB-separated text (: csv, tsv, txt).